Managing Multi-Region Deployments with Terraform Providers
Day 14: Working with Multiple Providers - Part 1
Mastering Terraform Providers: Multi-Region Deployment Strategies
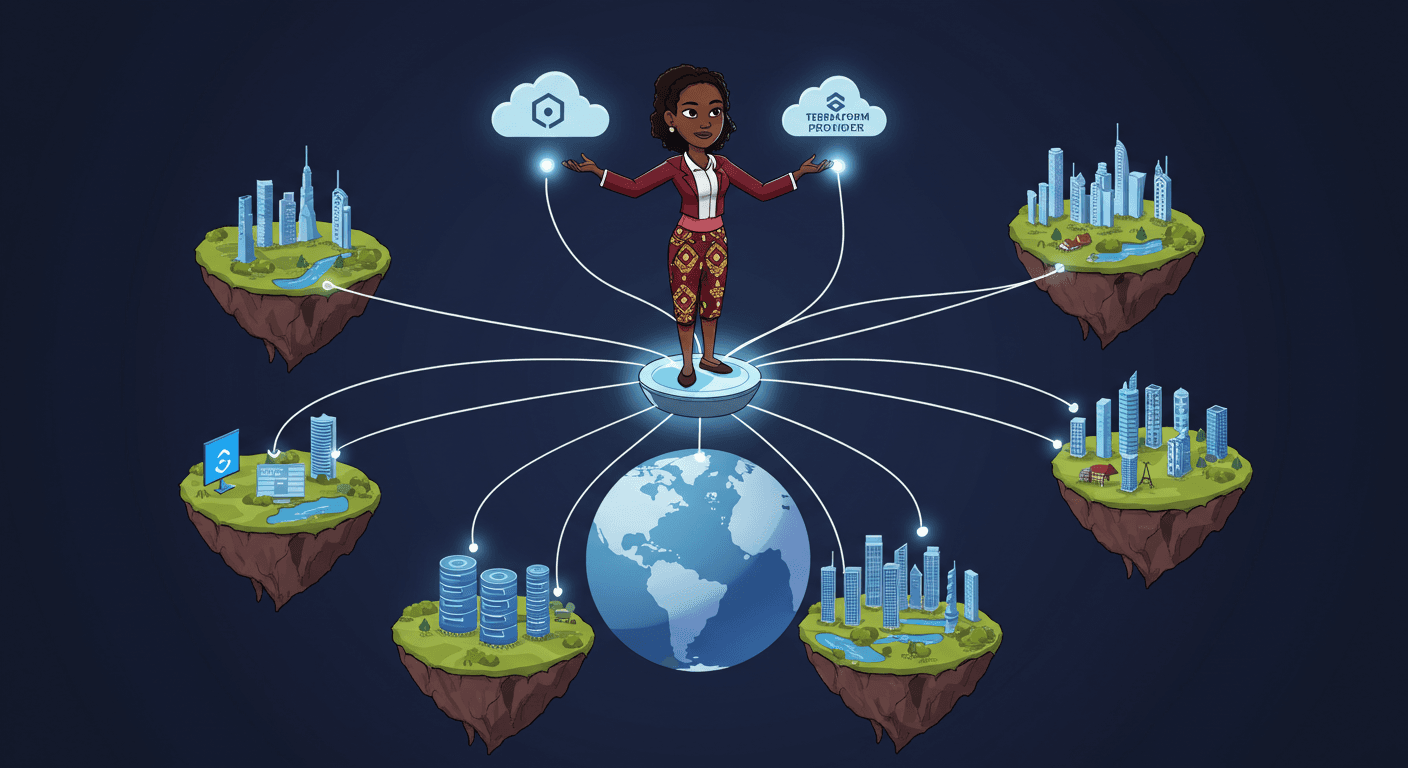
This week’s focus was Chapter 7 of "Terraform: Up & Running", covering essential concepts around Terraform providers, the plugins that enable Terraform to interact with cloud platforms, SaaS APIs, and other infrastructure services. Key sections included:
"What Is a Provider?" – Understanding how providers act as bridges between Terraform and external APIs.
"How Do You Install Providers?" – Exploring automatic vs. explicit provider installation methods.
"How Do You Use Providers?" – Configuring provider blocks and authentication.
"Working with Multiple Copies of the Same Provider" – Setting up provider aliases for multi-region or multi-account deployments.
Hands-on Learning
To reinforce these concepts, I completed two critical labs:
Lab 15: Terraform Testing – Ensured configurations were validated before deployment.
Lab 16: Terraform CI/CD Integration – Automated provider-based deployments in a pipeline.
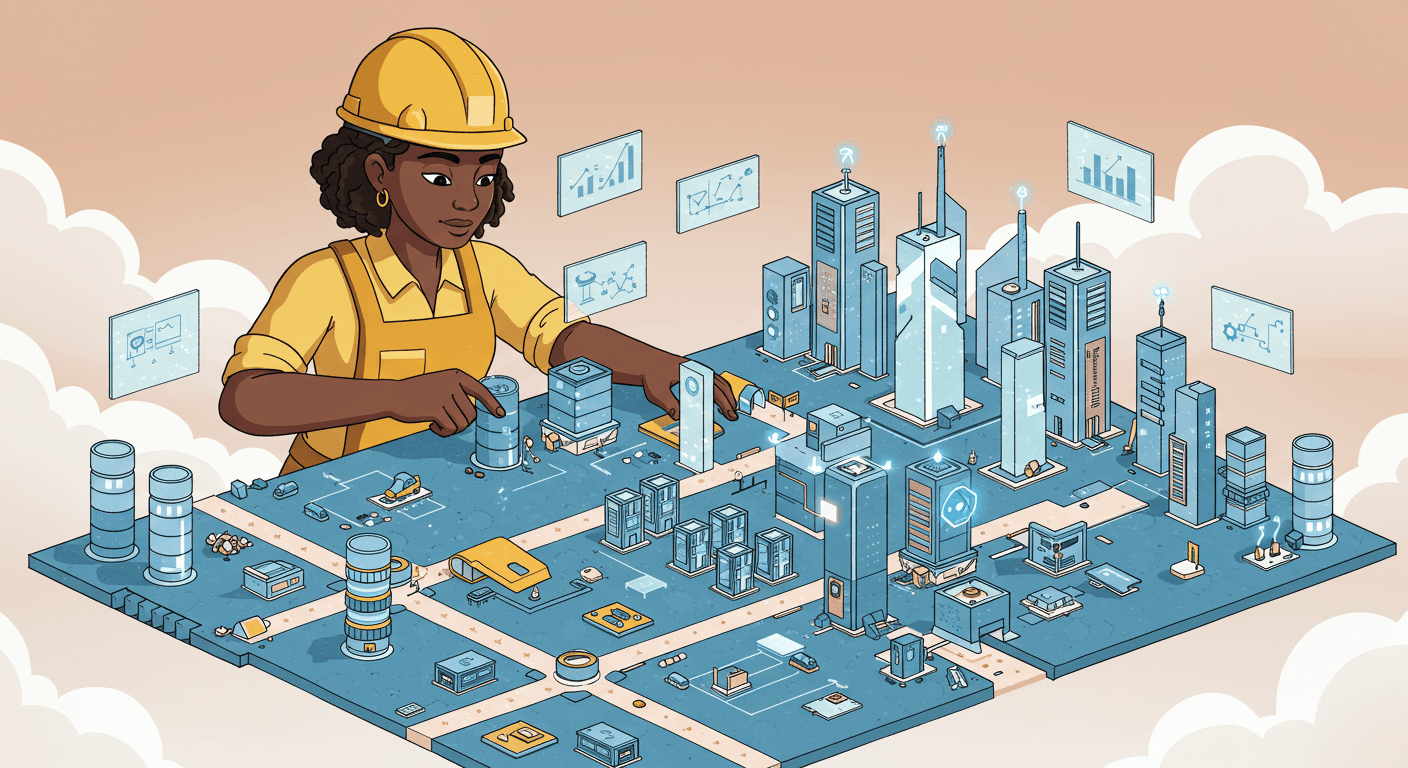
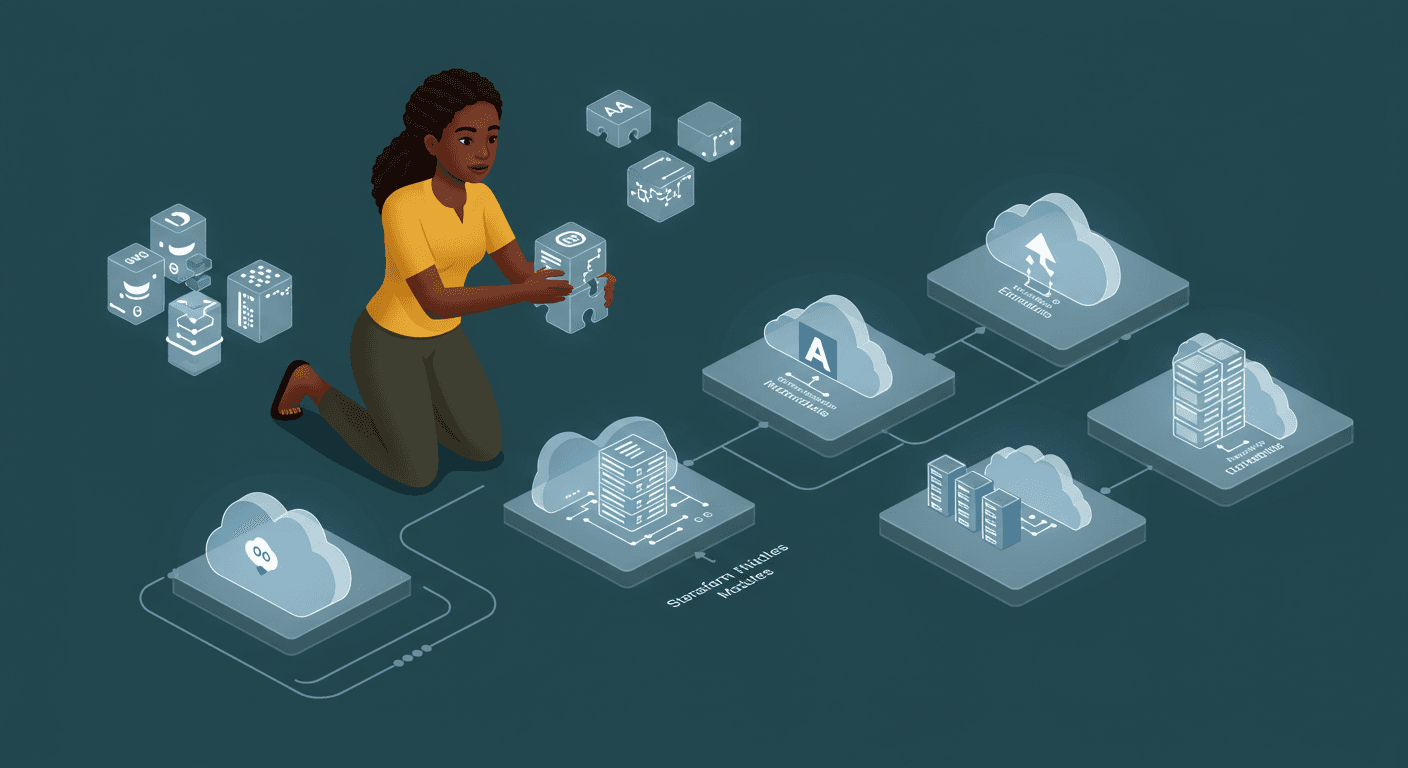
Implementing Multi-Region Deployments
One of the most powerful features of Terraform is the ability to manage multi-region infrastructure using provider aliases. Here’s how I implemented it:
1. Configuring Multiple AWS Providers
Instead of a single default provider, I defined multiple AWS provider instances with aliases for different regions:
provider "aws" {
region = "us-east-1"
alias = "primary"
}
provider "aws" {
region = "us-west-2"
alias = "backup"
}
This allows resources to be explicitly deployed in different regions by referencing the provider alias.
2. Conditional Multi-Region Deployment
To optimize costs, I implemented environment-based region selection:
locals {
use_multi_region = var.environment == "production" ? true : false
}
resource "aws_instance" "app_server" {
provider = aws.primary
# Only deploy in backup region if production
count = local.use_multi_region ? 1 : 0
# ... instance config
}
3. Region-Specific AMI Lookups
Since AMIs are region-specific, I used data sources to fetch the correct image per region:
data "aws_ami" "primary_ami" {
provider = aws.primary
owners = ["amazon"]
filter {
name = "name"
values = ["amzn2-ami-hvm-*-x86_64-gp2"]
}
}
data "aws_ami" "backup_ami" {
provider = aws.backup
owners = ["amazon"]
filter {
name = "name"
values = ["amzn2-ami-hvm-*-x86_64-gp2"]
}
}
4. Independent Secrets Management
Each region had its own AWS Secrets Manager entries, ensuring no cross-region secret leakage:
data "aws_secretsmanager_secret" "db_creds_primary" {
provider = aws.primary
name = "prod-db-credentials"
}
data "aws_secretsmanager_secret" "db_creds_backup" {
provider = aws.backup
name = "prod-db-credentials-backup"
}
Key Achievements
Multiple AWS Provider Configurations – Successfully deployed resources across regions using aliases.
Conditional Deployment Logic – Production environments span multiple regions, while dev/staging stay single-region for cost savings.
Region-Specific AMI Handling – Eliminated manual AMI ID updates with dynamic data sources.
Isolated Secrets per Region – No shared credentials between regions, improving security.
Cost-Optimized Strategy – Reserved instances in backup regions only for critical workloads.
Provider Aliases for Resource Targeting – Precise control over where resources deploy.
Region-Specific Tagging & Configs – Custom tags and settings based on regional requirements.
Lessons Learned & Next Steps
Key Takeaways
Provider Aliases Are Powerful – They enable complex multi-region, multi-cloud, and multi-account setups.
Avoid Hardcoding Region Dependencies – Use variables and data sources to keep configurations flexible.
Testing is Crucial – Multi-region setups introduce complexity—automated testing (Lab 15) is a must.
Future Improvements
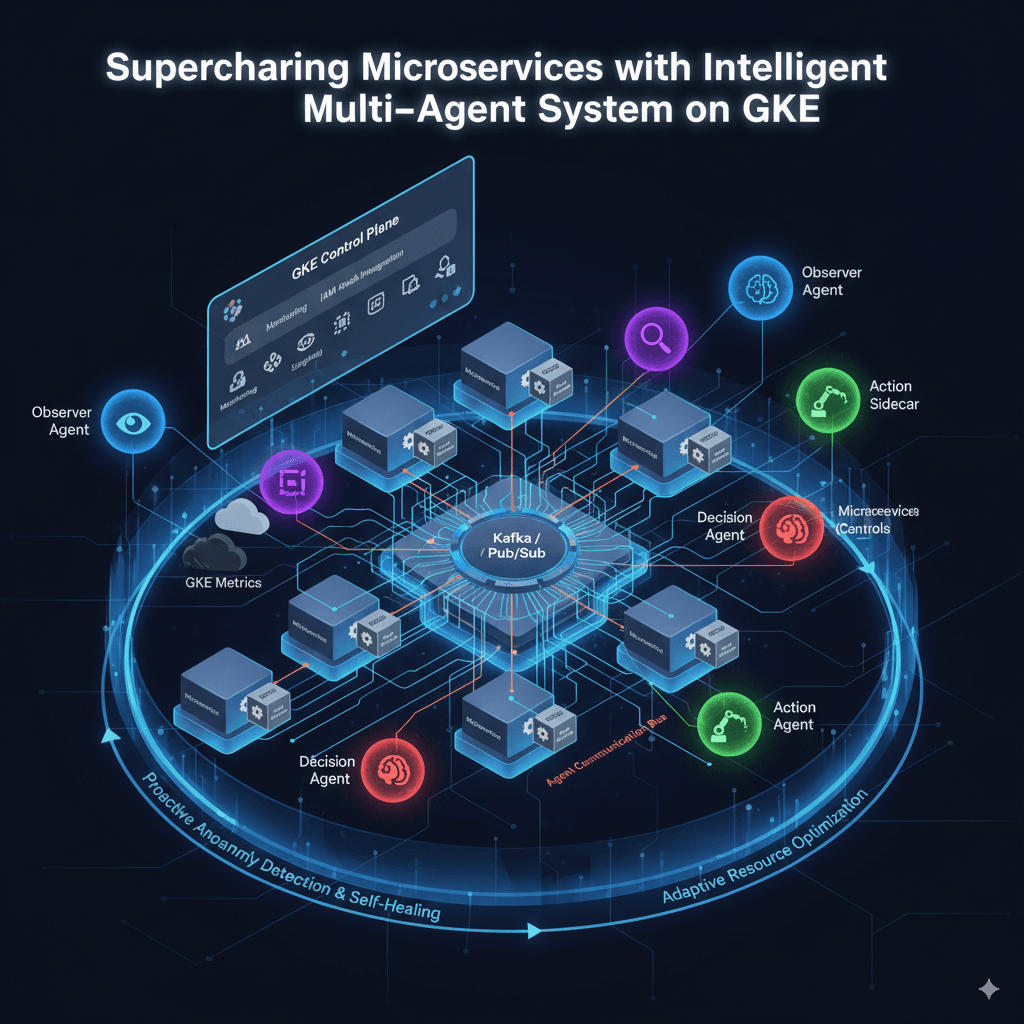
Multi-Cloud Expansion – Experiment with Azure & Google Cloud providers alongside AWS.
Dynamic Provider Selection – Use Terraform workspaces to switch providers based on deployment context.
Disaster Recovery Automation – Implement failover logic using Terraform + Route 53.