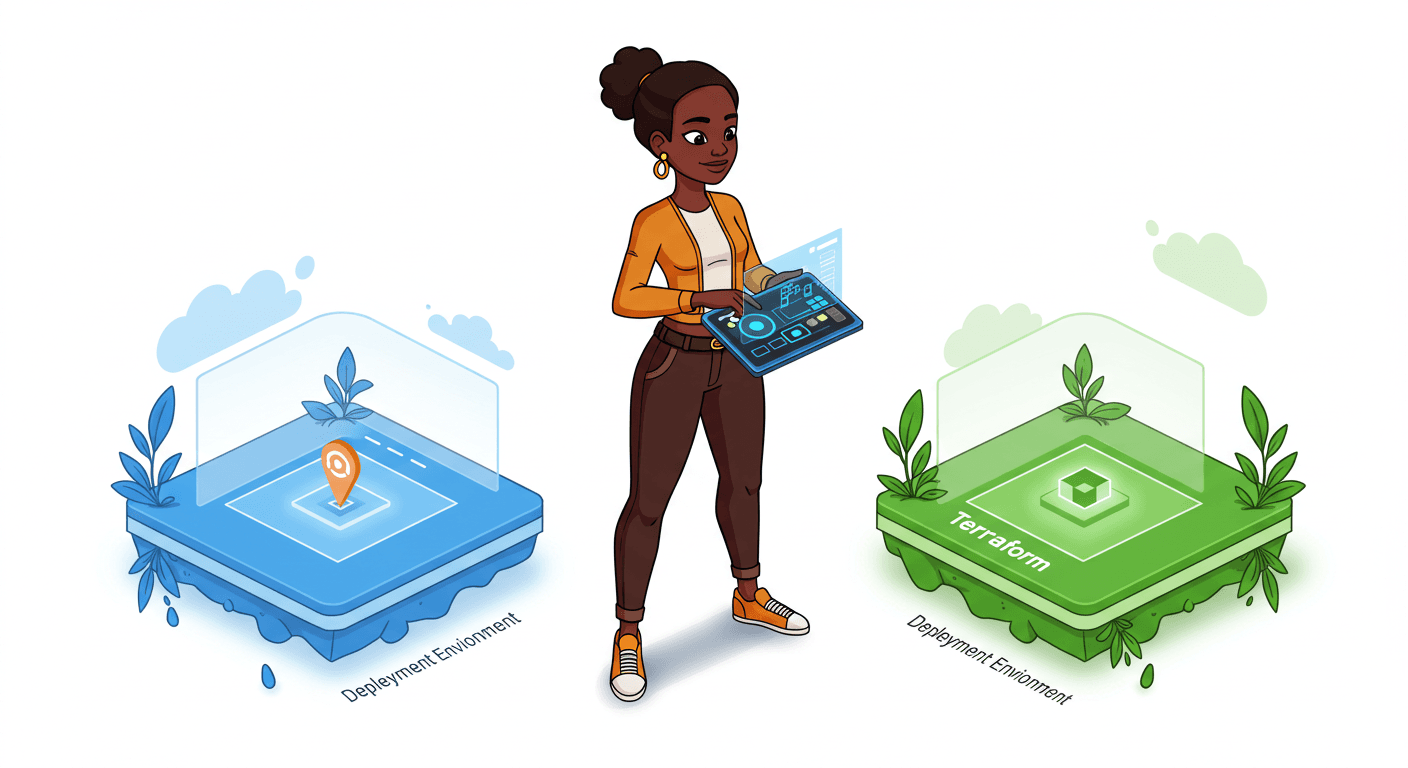
How to Implement Blue/Green Deployments with Terraform for Zero Downtime
Day 12: Zero-Downtime Deployment with Terraform
This week’s focus was on Chapter 5 (Pages 169-189) of our course material, which dives deep into Zero-Downtime Deployment Techniques. The chapter provided invaluable insights into maintaining system availability while rolling out updates.
To reinforce the theory, I completed two hands-on labs:
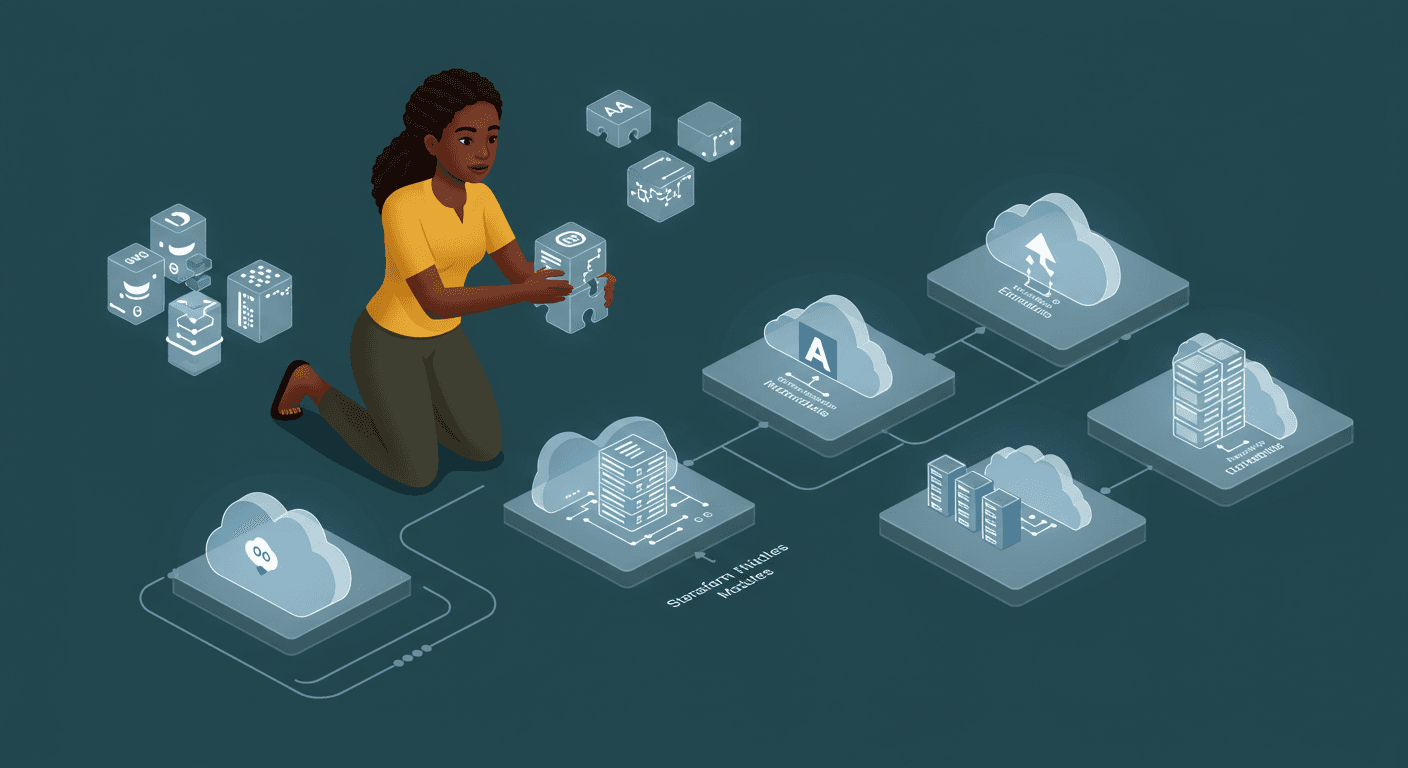
Lab 13: Module Composition – This helped me understand how to structure reusable Terraform modules for better maintainability.
Lab 14: Module Versioning – A crucial lab that taught me how to manage module versions effectively, ensuring stability across deployments.
Implementing Zero-Downtime Deployments
Moving from theory to practice, I successfully implemented several key techniques to achieve seamless deployments without service interruptions. Here’s how I did it:
1. Migrating from Launch Configurations to Launch Templates
Launch Configurations are now deprecated, so I transitioned to Launch Templates, which offer more flexibility and support newer EC2 features. This was the foundation for ensuring smooth instance replacements.
2. Lifecycle Rules for Safe Updates
By setting create_before_destroy = true, Terraform ensures that new resources are provisioned before the old ones are terminated. This simple yet powerful rule prevents downtime during updates.
3. Rolling Instance Refresh
AWS’s instance refresh feature ensures that only a controlled number of instances are replaced at a time. With a 90% healthy instance threshold, the system remains stable even during large-scale updates.
4. ELB Health Checks for Traffic Control
The Elastic Load Balancer (ELB) was configured with strict health checks, ensuring traffic is only routed to fully functional instances. This prevents users from hitting servers that are still initializing or failing.
5. Auto Scaling for Dynamic Capacity
Auto Scaling policies were fine-tuned to automatically adjust capacity based on CPU utilization, ensuring optimal performance without manual intervention.
Key Achievements
This implementation was about building a resilient, scalable, and secure infrastructure. Here’s what was accomplished:
Zero downtime deployments – Updates happen seamlessly, with no impact on end users.
Environment-specific logic – Different settings for dev, staging, and prod ensure safety and cost efficiency.
Production-grade security – Encrypted volumes and restricted SSH access keep the infrastructure secure.
Cost optimization – Using different instance types per environment (e.g., smaller instances for dev) reduces unnecessary spending.
Automated scaling – The system scales up or down based on real-time demand.
Load balancer integration – Health checks ensure only healthy instances serve traffic.
Final Thoughts
Transitioning to zero-downtime deployments was a mindset shift. By leveraging infrastructure as code (IaC) and AWS best practices, the system is now more reliable, scalable, and cost-effective.
If you’re working on similar challenges, my biggest takeaway is this: Test rigorously. Even the best automation can fail if health checks or thresholds aren’t properly configured. Simulate deployments in a staging environment before going live.